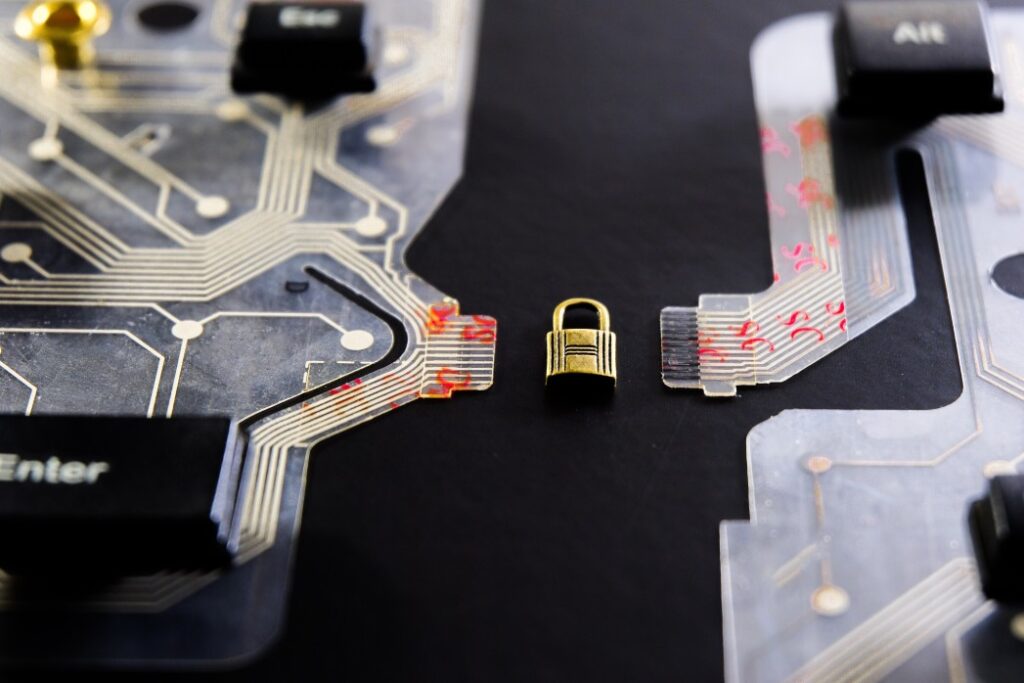
Cloud Security
Moving to the cloud can be a secure and cost effective idea. However, taking the time to evaluate organizational needs and readiness is a step that many organizations miss. IPS offers to review your data sensitivity to determine what control capabilities an organization should keep (a factor that plays into IaaS, PaaS and SaaS); reviewing the contract to ensure the cloud vendor is legally meeting expected compliance standards and organizational needs; and data transition to assist the organization in secure data uploads.
As a continued service IPS will audit the cloud system and report any changes or added risk to the Authorizing Official.



